Cyber Criminals are constantly looking for new and innovative ways to ensure their activity goes undetected. Phishing attacks in particular are becoming increasingly sophisticated, and recently we've seen a new type of attack in use against the University - SharePoint phishing.
How it works
The perpetrators create a document containing web links to either fake credential phishing pages, or malicious sites that will attempt to place malware on your device. They then upload the document to a legitimate file sharing service such as SharePoint, and share it with their would-be victims via email.
Why this is a threat
By uploading the document to a file sharing service, the perpetrator is able to separate the email payload from the recipient organisation’s infrastructure. This means the malicious content is far more difficult for automated defence tools to detect - the sender address of the email will be a valid SharePoint email address, and any links within the initial email will also be valid.
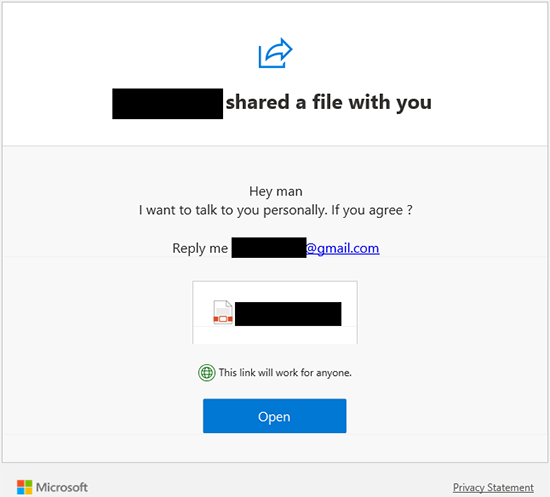
The screenshot below shows an example of a SharePoint Phishing email.
It is not until the document hosted on SharePoint is opened that the payload is delivered.
And it’s not only SharePoint. Perpetrators use other file sharing platforms such as WeTransfer, Google Drive, Drobox in the same way.
What should you do?
- Be suspicious. The best defence against this type of attack is to be suspicious of any unsolicited emails. Even if the apparent sender is known to you, always verify the email independently, particularly if you were not expecting files to be transferred.
- Report the email to IT by forwarding it to spam@abdn.ac.uk so that the threat can be eradicated for any other recipients.
Find out more
You’ll find more information on protecting yourself and the University from Cybercrime in Toolkit’s Information Security resource.
Author: Information Security Team, DDIS


