Working with DaSH
Each bespoke project registered with DaSH will progress through the seven project stages:
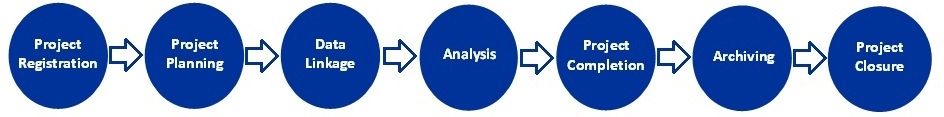
Detailed information about each stage of the project is included below.
DaSH Project Lifecycle
- Project Registration & Planning
-
Enquiries to DaSH and initial meeting
Researchers who are considering undertaking a data linkage or hosting study should contact DaSH via DaSH@abdn.ac.uk . A project reference number (e.g. DaSHXXX) will be assigned. Please use this project number in all communications with DaSH.
DaSH will then email you a Project Initiation Document (PID) to complete prior to an initial meeting which is designed to gather further information on your proposed project.
DaSH Project Support
Once the feasibility of your project has been confirmed, DaSH will provide support with:
- Funding Applications: A costing will be provided for the DaSH component of your study (including costs for facility use, data management / technical support, governance / administrative support, etc.).
- Datasets and Data Requirements: Assistance will be provided with the planning and design of the study, identification of relevant datasets and development of a data specification for extracting, linking and formatting the research data.
The range of datasets often used for linkage studies include the University held Aberdeen Maternity and Neonatal Databank (AMND) , the national Scottish health records data held at NHS Information Services Division (ISD) , disease specific cohorts held nationally such as Scottish Care Information - Diabetes Collaboration , or others held by the researchers undertaking the data linkage studies. To view a larger list of University hosted datasets, visit the ACHDS datasets page
- Project permissions: Advice and input for funding and permissions applications will be provided. A Permissions Pathway guide explaining the approvals process can be obtained from DaSH.
If you are a local researcher (i.e. University of Aberdeen or NHS Grampian employee) wishing to access local NHS Grampian data, then North Node Permissions Advisory Committee ([ NNPAC]) approval may be suitable. DaSH will be able to advise on whether your planned study meets the criteria.
The team will also assist you in the preparation of a Data Management Plan (DMP) and Data Linkage Plan (DLP) for your project. These documents illustrate the data flow, access conditions and researchers. The DMP and DLP are useful for funders and permissions providers.
- Approved Researcher requirements: Guidance will be provided on criteria for Approved Researchers accessing DaSH. This includes:
- Employment by an approved institution (e.g. NHS, Scottish Government, university or local authority).
- For commercial projects, there will be a requirement for a contractual partnership with an approved research organisation. DaSH can provide advice on this.
- A valid certificate for an approved information governance training course will be required for the duration of the research project. Please see below for a link to an approved course:
- MRC Research, GDPR and Confidentiality Module (free e-learning)
- A signed DaSH investigator declaration for the study (usually signed by the study PI or equivalent, and if appropriate, the student researcher) is also required.
- Data Linkage
-
Prior to Linkage
Once funding and permissions are in place, and ahead of data being transferred to or from DaSH, a DaSH Research Coordinator will arrange a 'Pre-linkage" meeting with the Data Analysts. This meeting is designed to allow researchers to meet with the Data Analyst for their project, to discuss technical aspects and specifications, and to plan the project schedule with the analyst team. This meeting will ensure that the cohort is fully specified, along with ensuring the correct dataset variables have been selected.
Linkage
In the linkage stage, your Data Analyst will create an extraction code based upon your cohort requirements and variables required for your project. If this involves more than one dataset, the cohort will be linked. If the project requires datasets not held locally by DaSH, the Analyst will coordinate with the relevant data custodians, ensuring secure transfer of data and that any data received is properly cleansed and put into the correct output format. Data will be pseudo-anonymised to ensure individual patient privacy regulations are adhered to. All work is checked by a second Analyst and signed off by a DaSH lead before release to researchers.
Getting Your Linked Research Data File
Once a file is ready for you in your Safe Haven folder, you will be notified by the DaSH team. Prior to accessing the folder, your Research Coordinator will arrange a 'Pre-Access' meeting. This meeting is designed to ensure that all Researchers gaining access to the Safe Haven are aware of their responsibilities. It also allows for any questions to be addressed.
Once in the Safe Haven, you will need to validate your data and check it against your data specification documentation to ensure it meets your requirements. It is useful to check your data as soon after receiving the files as possible. That way, your analyst in the Safe Haven (and the external data source provider) will be able to address issues quickly.
- Analysis
-
Within the Safe Haven, your project receives a dedicated secure folder where the research team can safely analyse their data without the ability to copy, print, or transfer data outside the Safe Haven. The Safe Haven has a number of statistical and analytical tools available for all researchers, listed under our services . If your project requires bespoke applications, extensions or libraries, the Dash Analysts will work with the Directorate of Digital Information Services to ensure that these can be allowed within the Safe Haven or can suggest alternative tools to work with that meet the information security requirements of the Safe Haven. Researchers also have access to any bespoke code that have been written that can be run within a statistical package.
Once researchers are ready to publish findings, researchers submit a request for release of the data to be released from DaSH. Patient-level data cannot leave DaSH; instead, aggregated results are allowed with a minimum number of records whilst also ensuring that individual patients cannot be identified in aggregated results.
- Project Completion, Archive and Closure
-
At the end of a project, it is the Principal Investigators responsibility to complete any required end of study reports (e.g. as requested by ethics or data custodians). Please note that projects which are 'completed' via sponsor cannot subsequently be amended. Therefore, if you wish to access your data for follow up work, extensions to project end dates should be sought when required.
DaSH will contact researchers at the end of the analysis period to confirm that the project can be closed and archived. The standard DaSH archiving period is 5 years, unless previously agreed with DaSH.
- Responsibilities & Data Disclosure
-
Researcher Responsibilities
Researchers should ensure they read and adhere to the rules and responsibilities outlined in their project Data Management Plans, Investigator Declaration and access instructions.
This includes the following:
- Data should not be shared with anyone who is not a named user in the documents provided to permissions bodies who granted approvals for the study.
- No attempt will be made to reuse the data for commercial purposes beyond those stated in the documents provided to permissions bodies who granted approvals for the study.
- Approved Users are responsible for reporting to DaSH, without delay, any unintentional disclosure of information from their safe haven project folder.
- Approved Users will not attempt to identify any individual within the study data.
- Only research outputs that have been approved as non-disclosive by DaSH can be used as part of presentations, publications, papers and analysis.
- Approved Users and other members of the project's research team will not discuss information which could breach an individual's privacy in a public place, in this context a public place may be taken to be anywhere people not directly involved in the study may be present.
- Approved Users will not share their safe haven login password with any other person.
- Approved Users will remotely access DaSH only in suitable locations where on-screen work cannot be read by anyone not named as an Approved User.
- Workstations must not be left unattended, either log out of the safe haven or lock the computer.
- Researchers cannot transfer or copy by any means (e.g. electronically, manually or by generating print outs) individual patient data out with the DaSH secure folder.
Data Release and Disclosure
If you wish to remove outputs from the safe haven, the only method of removing results, outputs or information from your safe haven folder is to contact DaSH via DaSH@abdn.ac.uk and provide the names of the files/folders you want released. They will then be assessed by a DaSH Research Coordinator (or named statistician if appropriate) for risk to patient confidentiality prior to release.
Generally, outputs requested for release should:
- Be 'publication-ready' (e.g. tables / graphs / text rather than excessive SPSS outputs)
- Not include patient level data, however aggregated results can be released once approved by a DaSH Research Coordinator.
- Not include small numbers (generally <5)
- Security
-
DaSH has been accredited by the Scottish Government (November 2017) and meets the Information Security and Governance standards outlined in the Charter for Safe Havens in Scotland 2015 . Additionally, DaSH is accredited to ISO27001:2013 Information Security Management
Custodians
The DaSH approach ensures that researchers responsible for the custodianship of a dataset can retain rigorous control over who has access to their research data and a researcher cannot pass on the data without prior approvals. This is crucial to ensure that data is not subsequently combined with other data sources resulting in possible identification of individual patients.
Dedicated Servers
DaSH comprises of state-of-the-art dedicated computer servers to safely store patient and public data. Identifiable data, crucial to enabling linkage of different datasets together, is stored within a dedicated NHS DaSH server, to the highest levels of security, whist the Virtual Private Network (VPN) and data storage server sits in the University of Aberdeen data centre. Access to these servers is controlled by the respective IT Departments.
The Linkage Process
During the linkage process, one analyst extracts the cohort from the various datasets that the university holds and then assigns a pseudo-anonymised link number. This is then sent to the appropriate department, in the majority of cases NHS National Services Division (ISD), who then extract the data required and create a new file without the identifiable information, just the pseudo-anonymised link number. This new file is then sent to a second analyst, who is not privy to the identifiable information, who then performs any additional linkage and a sense test before moving it into the dedicated area within the Safe Haven.
Sense Tests and Disclosure Checks
A sense test is performed before data release to allow for any possible mismatch in linkage to be identified. We also use this test to highlight any disease specific groups with small numbers of people. Expert advice is sought to determine whether there is a potential risk to patient confidentiality in the event that the disease is rare or uncommon.
Restricted Access
Through DaSH, researchers safely access their data for analysis without the ability to copy, print, or transfer data outside the Safe Haven in anyway. Researchers access their data for analysis via the VPN in a dedicated secure folder within the Safe Haven and data is only released once DaSH is sure that all of the necessary approvals and permissions are in place and checks have been carried out.
Quality Assurance
Our staff ensure that each project has all the relevant paperwork completed and that the data is processed in line with the data management plan, data linkage plan and DaSH working protocols for security.
